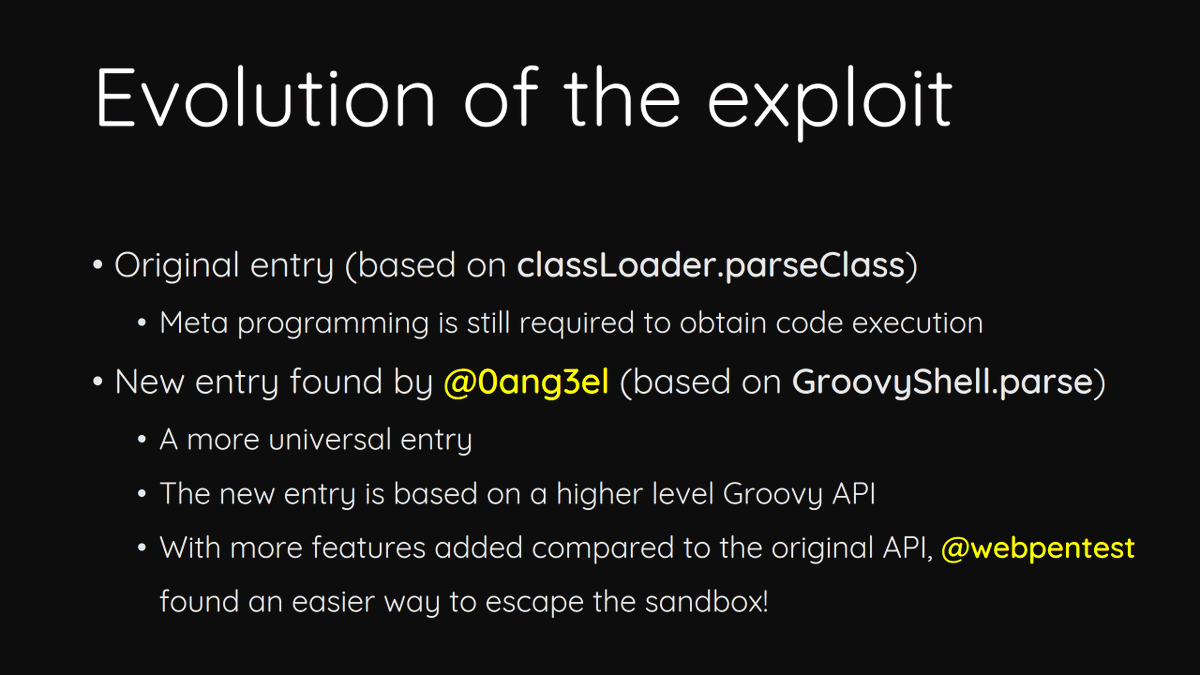
In this section, we explain what OS command injection is, and describe how vulnerabilities can be detected and exploited. We also show you some useful
OS Command Injection in Web App Penetration Testing, 2023, by Karthikeyan Nagaraj

How to detect and prevent command injection attacks?

How to Prevent Blind Command Injection
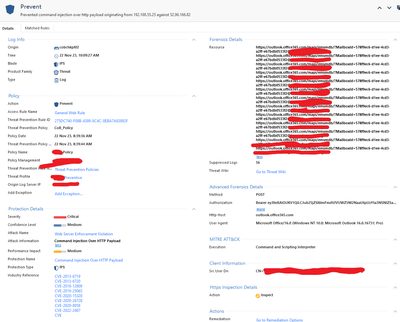
Solved: Command Injection Over HTTP Payload - Check Point CheckMates

x WiCyS CTF 2023
Black Hunter (f0rever_hunter@) / X

Mohit Yadav (@mohitchichi88) / X

Sensors, Free Full-Text
4 essentials to prevent OS command injection attacks
How to Prevent SQL Injection - Cloudbric

What Is an OS Command Injection?